Every quarter, someone on your team spends days pulling STIG checklist results into spreadsheets just to answer one question: are we compliant? That time ends today.
The Real Problem With STIG Compliance Reporting
Most programs already have the data. STIG checklists are being completed. CKL and CKLB files exist. The problem isn't the checklist work — it's what happens after.
The results sit in exported files. Someone opens them manually, cross-references the findings, builds a spreadsheet, and turns it into a briefing for the ISSO or AO. Every quarter. The same process, over and over.
This is a data pipeline problem. And Splunk is a data pipeline tool.
What This Looks Like When It Works
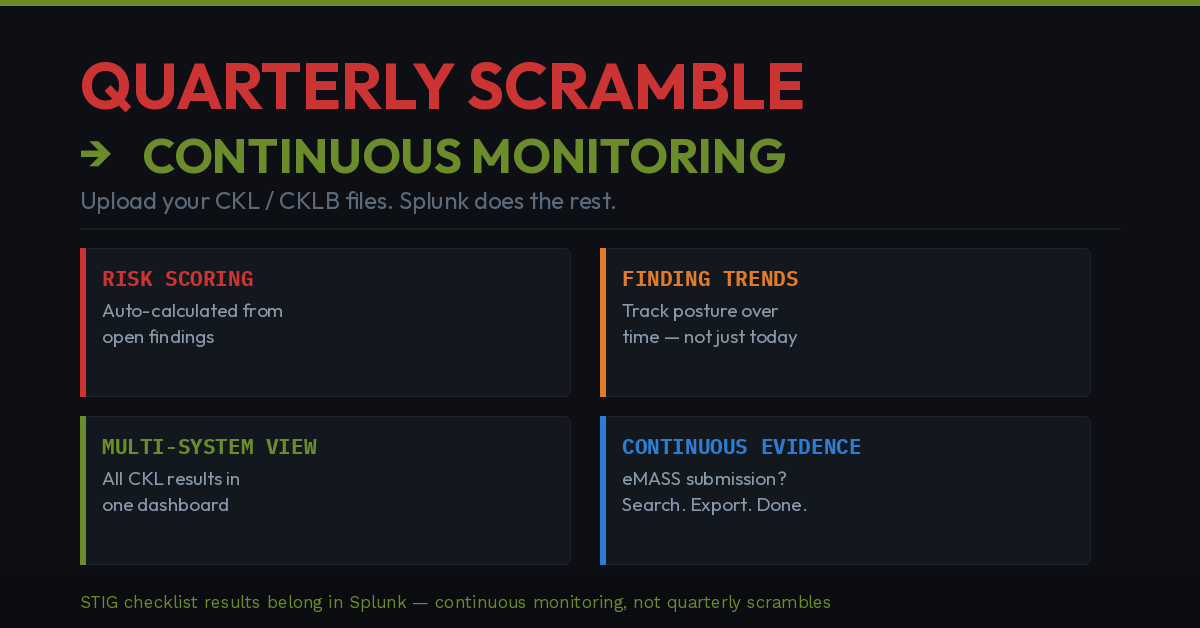
When STIG checklist results flow directly into Splunk, a few things change.
First, the data is searchable. Instead of opening a CKL file, you run a search. Instead of building a spreadsheet, you load a dashboard. The compliance question — where are our open findings, what is our risk posture — gets answered in seconds, not days.
Second, you get trending over time. A single checklist tells you where you stand today. Checklists in Splunk tell you whether your posture is improving, degrading, or holding steady across your environment. That's the conversation your AO actually wants to have.
Third, the evidence is already there. When the eMASS submission is due or an audit is underway, your compliance history is in Splunk. You're not reconstructing posture from saved spreadsheets and email threads.
Why This Matters in DoD and Federal Environments
STIG compliance isn't optional in DoD and federal civilian programs. It's a condition of authorization. Demonstrating ongoing compliance — not just at ATO time but continuously — is an expectation of RMF. The programs that do this well have turned compliance reporting from a quarterly scramble into a routine search.
The gap most programs have is not in completing the checklists. It's in aggregating results across multiple systems, tracking open findings over time, and producing defensible evidence of continuous monitoring without manual effort every reporting cycle.
The Data Source That Makes This Possible
STIG checklists output CKL and CKLB files. Those files contain your full compliance posture against a defined control set — every check, every status, every finding. Ingesting those files into Splunk and building dashboards on top of them gives you environment-wide STIG visibility without rebuilding it from scratch every quarter.
I built a free Splunk app that handles this:
STIG Compliance App → splunkbase.splunk.com/app/8486
CKL and CKLB file upload, four compliance dashboards, automated risk scoring across your environment. Free on Splunkbase today.
The Bigger Point
Whether you use this app or build your own solution, the pattern is worth considering: STIG checklist results belong in your SIEM, not in a spreadsheet. If you're already completing checklists and already running Splunk, the pipeline between them shouldn't require manual work every reporting cycle.
Are you managing STIG compliance reporting in Splunk today? Drop your approach in the comments — I'd like to hear how others are solving this.